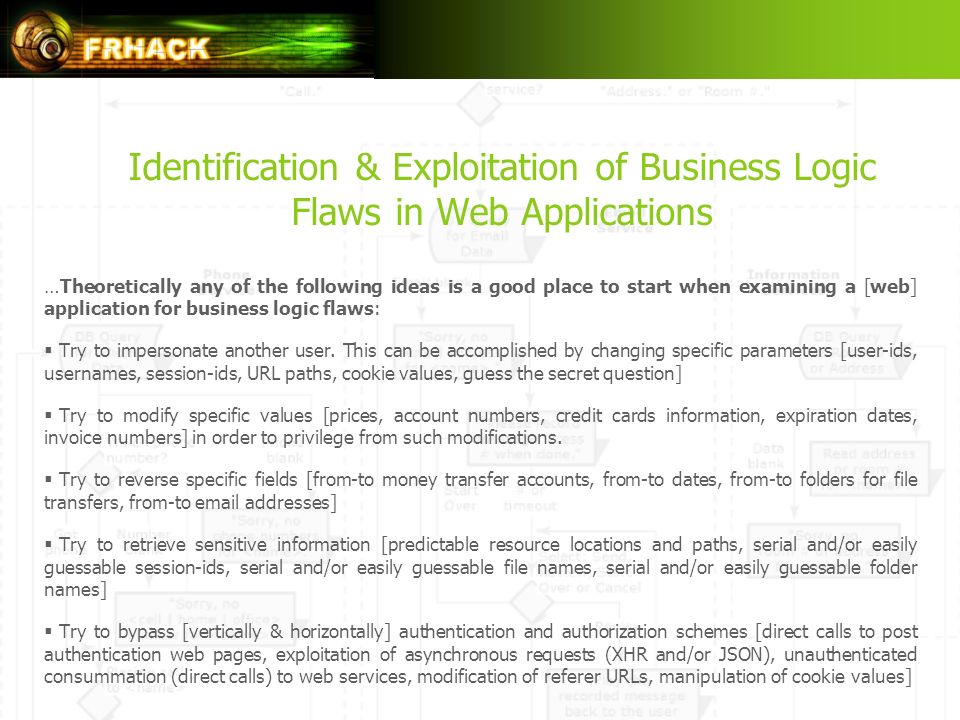
Identification & Exploitation of Business Logic Flaws in Web Applications Filippos Georgiadis (MScIS, CISSP, CISA) Security Engineer Cosmote Mobile Telecommunications. - ppt download

MySQL / PHP Database Applications: Bulger, Brad, Greenspan, Jay, Wall, David: 9780764549632: Amazon.com: Books
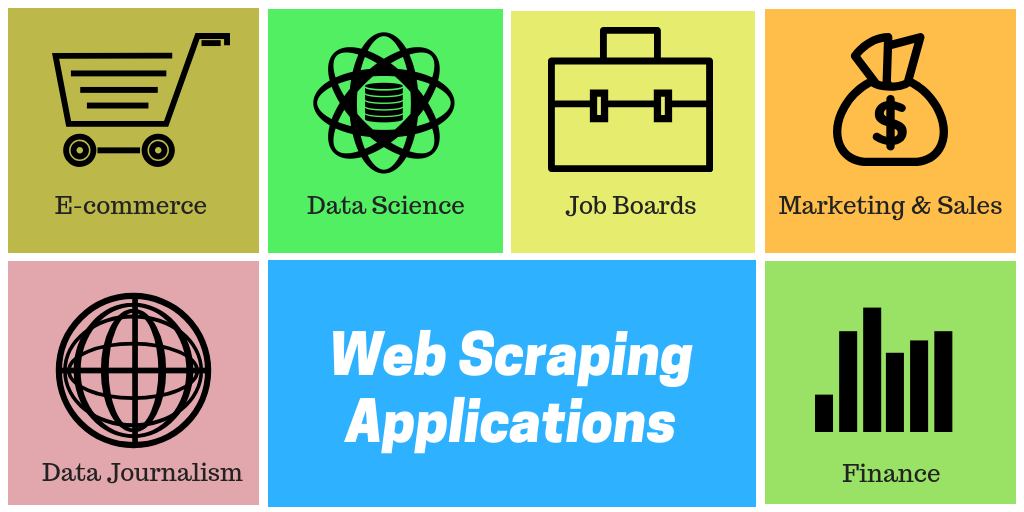
How Web Scraping is Transforming the World with its Applications | by Hiren Patel | Towards Data Science